20 Best Pieces Of Advice For Deciding On Shielded Sites
Wiki Article
The ZK-Powered Shield: What Zk-Snarks Shield Your Ip As Well As Id From The Public
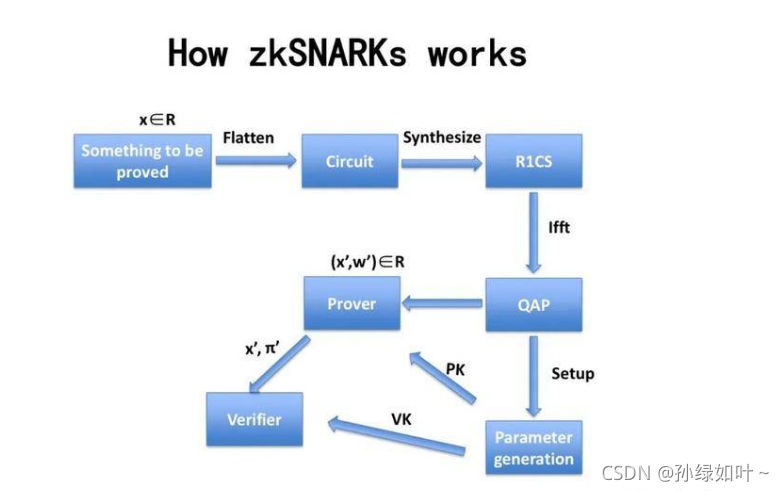
For many years, privacy instruments function on a principle of "hiding within the crowd." VPNs direct you through a server. Tor sends you back and forth between multiple nodes. They are efficient, however the main purpose is to conceal your source of information by moving it but not proving it isn't required to be disclosed. Zk-SNARKs (Zero-Knowledge Short Non-Interactive Arguments of Knowledge) introduce a very different concept: you can prove you are authorized to do something without revealing which authorized entity that you're. In Z-Text, this means the ability to broadcast messages through the BitcoinZ blockchain. The network will confirm you're legitimate as a person with a valid shielded address, but it cannot determine which particular address broadcast it. Your IP address, your identity as well as your identity in the exchange becomes unknowable mathematically to anyone watching the conversation, and yet confirmed to the protocol.
1. The Dissolution Of the Sender-Recipient Link
The traditional way of communicating, even when it is using encryption, makes it clear that there is a connection. Uninitiated observers can tell "Alice is talking to Bob." zk-SNARKs break this link entirely. When Z-Text releases a shielded transactions and the zk-proof is a confirmation that this transaction is legal--that the sender's balance is adequate and the correct keys--without revealing the sender's address or the recipient's address. To an observer outside the system, this transaction appears as security-related noise that comes directly from the network, in contrast to any one particular participant. The link between two specific humans becomes computationally impossible to identify.
2. IP Address Protection at the Protocol Level, Not at the Application Level.
VPNs as well as Tor protect your IP in the process of routing traffic via intermediaries. However those intermediaries become new points of trust. Z-Text's usage of zkSNARKs indicates that your IP's location is never relevant to transaction verification. If you broadcast your secret message to the BitcoinZ peer-to-peer network, you belong to a large number of nodes. The ZK-proof makes sure that when a person is monitoring the transmissions on the network, they cannot determine whether the incoming packet in the same way as the specific wallet is the originator, as the certificate doesn't hold that information. The IP disappears into noise.
3. The Elimination of the "Viewing Key" The Dilemma
In most blockchain privacy systems with an "viewing key" with the ability to encrypt transaction information. Zk -SNARKs, as they are implemented in Zcash's Sapling protocol used by Z-Text allows selective disclosure. You can prove to someone the message you left that does not divulge your IP address, all of your transactions or even the entire content of the message. The proof itself is all that is shared. A granular control of this kind is impossible with IP-based systems, where the disclosure of the content of the message automatically exposes the identity of the sender.
4. Mathematical Anonymity Sets That Scale globally
When you are using a mixing or a VPN Your anonymity is restricted to other users in the specific pool at the time. By using zk-SNARKs your privacy is will be guaranteed by every shielded address on the entire BitcoinZ blockchain. Because the verification proves the sender is a secured address, one of which is potentially millions, but doesn't give a indication of which, your anonymity is the same across the entire network. Your identity is not hidden in any one of your peers however, you are part of a massive community of cryptographic identifications.
5. Resistance to attacks on traffic Analysis and Timing attacks
The most sophisticated attackers don't just look at IP addresses. They analyze their patterns of communication. They determine who's transmitting information at what times, and compare to the exact timing. Z-Text's use with zk SNARKs in conjunction with a blockchain-based mempool, permits the separation of an action from broadcast. A proof can be constructed offline and then broadcast it as a node will transmit it. The date of inclusion in a block is inconsistent with the point at which you made the proof, impairing the analysis of timing that typically can be used to defeat simpler tools for anonymity.
6. Quantum Resistance via Hidden Keys
The IP addresses you use aren't quantum-resistant; if an adversary can observe your activity as well as later snoop through the encryption the attacker can then link them to you. Zk's-SNARKs which is used in Z-Text, shield your keys by themselves. Your public keys will not be displayed on blockchains as the proof verifies that you have the correct key while not revealing the actual key. Quantum computers, later on, could look only at the proof and not the actual key. Your private communications in the past are protected as the password used to secure them wasn't exposed to cracking.
7. Unlinkable Identities in Multiple Conversations
With a single wallet seed You can also generate multiple secured addresses. Zk-SNARKs can prove that you own one of these addresses without disclosing which. That means that you could have the possibility of having ten distinct conversations with ten different people. Moreover, no individual, or even the blockchain itself can link those conversations to the exact wallet seed. The social graph of your network is mathematically splined due to design.
8. Abrogation of Metadata as a target surface
Spy and regulatory officials often tell regulators "we don't have the data or the metadata." It is true that IP addresses represent metadata. People you contact are metadata. Zk SNARKs are distinct among privacy solutions because they disguise metadata on a cryptographic level. The transaction itself contains no "from" and "to" fields that are plaintext. It is not a metadata-based subpoena. The only thing that matters is evidence, and that can only prove that a legal incident occurred, not who.
9. Trustless Broadcasting Through the P2P Network
When you use a VPN you are able to trust the VPN provider to not log. When using Tor then you trust the exit node not to trace you. With Z-Text you send your zk-proof transaction on the BitcoinZ peer-to'-peer community. There are a few random networks, share the details, then break off. The nodes don't learn anything because the data does not prove anything. They cannot even be certain that you're who initiated the idea, given that you may be doing the relaying on behalf of another. The internet becomes a trustworthy provider of personal information.
10. "The Philosophical Leap: Privacy Without Obfuscation
Furthermore, zk's SARKs provide some kind of philosophical leap, to move from "hiding" towards "proving by not divulging." Obfuscation techniques recognize that the truth (your IP address, or your name) can be dangerous and needs to be concealed. Zk-SNARKs acknowledge that the truth cannot be trusted. Only the protocol needs to acknowledge that you're registered. The transition from reactive concealment and proactive relevance forms the basis of ZK's shield. Your identity, IP address and location do not remain hidden. They are essential to the nature of a network and therefore never requested in any way, nor are they transmitted, or exposed. Have a look at the most popular shielded for more recommendations including encrypted text app, encrypted text message, messages messaging, private text message, encrypted messages on messenger, private message app, private text message, purpose of texting, text privately, encrypted messenger and more.
"The Mutual Handshake: Rebuilding Digital Trust in an Zero-Trust World
The internet is built on an unintentional connection. Anyone can write to anyone. Anyone can be a follower on social media. Such openness, however valuable however, has led to a loss of confidence. Security, fraud, and harassment are all results of a process where connecting isn't a requirement for consent. Z-Text transforms this idea through the reciprocal cryptographic handshake. Before a single bit data exchanges between two individuals each must expressly agree to the transfer, and this consent is ratified by the blockchain. It is then confirmed with Zk-SNARKs. The simple requirement of mutual consent on the protocol level - builds digital faith from the ground up. It has the same effect as physical communication and says that you will not be able to speak with me until I've acknowledged my presence. I'm not able talk to you before you acknowledge me. In an age of zero trust, the handshake is the basis of communication.
1. The handshake as the Cryptographic Ritual
With Z-Text, the handshake isn't simply a "add contact" button. The handshake is actually a cryptographic procedure. The Party A submits a connecting request that contains their own public key as well as a temporary temporarily-ephemeral email address. Party B then receives the request (likely through a open post) and produces an acceptance, which includes their public key. Parties B and A then come up with a secret shared between them that defines the communication channel. The ceremony makes sure that both parties were actively participating while ensuring that no intermediary can enter the channel without being detected.
2. "The Death of the Public Directory
It is because emails and phone numbers belong to public directories. Z-Text doesn't have any public directories. Your Z-address will never be published to the blockchain. It hides inside the shielded transactions. Any potential contacts should have some information about you -- your public identity, a QR code, or a shared key to get the handshake. There's no search option. This is the main reason to send unsolicited messages. You cannot spam someone whose email address is not available.
3. Consent to be used as Protocol However, it is not Policy
On centralized platforms, it is possible to consent in centralized apps. It is possible to block someone once you have contacted them, but they've already entered your inbox. Consent is embedded into the protocol. Any message that is sent out must have an initial handshake. Handshakes are a negligible proof that both individuals have agreed on the connection. That means that the protocol can enforce consent instead of allowing you to react to its non-conformity. The design itself is considerate.
4. The Handshake as a Shielded Time
Since Z-Text employs zk SNARKs, the handshake itself is private. When you accept a connect demand, that connection will be protected. Any person watching can't tell your and an additional party has established a relationship. Your social graph becomes invisible. It is a handshake that takes place in dimness, visible only by one or both of them. This is the opposite of LinkedIn or Facebook which every interaction will be broadcast to the world.
5. Reputation without Identity
What do you need to know about who you should shake hands with? Z-Text's model allows for the emergence of reputation systems that doesn't depend on divulging the identity of an individual. Since connections are not public, it is possible to receive a handshake request from someone who shares one of your contacts. This common contact may be able to vouch against them using a cryptographic attestation, with no disclosure of who any of you. This trust can be viewed as a zero-knowledge and transitory: you can trust someone by relying on someone who you trust to trust that person without ever knowing about their identity.
6. The Handshake is a Spam Pre-Filter
With the requirement for handshakes even a zealous spammer can possibly request thousands of handshakes. Each handshake, similar to every message, demands an additional micro-fee. Spammers now face the same financial hurdle at the contact stage. In order to request one million handshakes, they need around $30,000. In the event that they want to pay for it, they'll still require you in order to give them. With the handshake, you create two obstacles to economic growth that is financially crazy for mass outreach.
7. Transparency and Reconstruction of Relationships
Once you've restored your ZText authenticity from the seed phrase Your contacts will be restored as well. What is the way that Z-Text can recognize who the contacts are with no central server? Handshake protocol records an insignificant, encrypted file to the blockchain--a note that an association exists between two shielded addresses. After you restore your wallet is scanned for these handshake notes and builds your contacts list. Your social graph will be stored on the blockchain, but readable only by you. Your relationships are as portable like your cash.
8. The Handshake as a Quantum -Secure Requirement
The handshake between two people establishes a mutually shared secret between two people. The secret information can be used to obtain keys in the future communication. Since the handshake itself is an event shielded from disclosure that never divulges public keys, it is invulnerable to quantum decryption. An adversary cannot later crack your handshake, revealing that the handshake left no public key exposed. The promise is eternal, yet it's invisibility.
9. Revocation and the Handshake that is not signed.
A trust breach can occur. Z-Text allows for a "un-handshake"--a cryptographic cancellation of the relationship. If you stop someone from communicating, your wallet announces a "revocation" evidence. This proof tells the network that messages to the blocked party should be ignored. Due to the fact that it's on-chain the decision to revoke is permanent and can't be rescinded by another party's clients. The handshake is able to be reversed with the intention of undoing it equally valid and verifiable as the initial agreement.
10. Social Graph as Private Property Social Graph as Private Property
Finally, the mutual handshake transforms who holds your social graph. In centralized networks, Facebook or WhatsApp have the data of what people communicate with who. They mine it, analyze it, and market it. The Z-Text social graph is protected and stored in the blockchain. The data is readable only by the user. It isn't owned by any corporation. of your contacts. It is a handshake that ensures the one and only proof of connection remains with you and your contact. Your information is secured cryptographically against the outside world. Your network is your property, not a corporate asset.